In the ever-evolving landscape of cybersecurity, protecting your organization from threats is paramount. One of the most effective tools in this arsenal is the Sentinel One Agent. This powerful endpoint protection platform offers comprehensive security solutions that go beyond traditional antivirus software. By leveraging advanced machine learning algorithms and behavioral analysis, the Sentinel One Agent provides real-time threat detection and response, ensuring that your systems are safeguarded against a wide range of cyber threats.
Understanding the Sentinel One Agent
The Sentinel One Agent is designed to be a lightweight yet robust security solution that can be deployed across various endpoints, including desktops, laptops, servers, and mobile devices. Its primary function is to detect, prevent, and respond to cyber threats in real-time. Unlike traditional antivirus software that relies on signature-based detection, the Sentinel One Agent uses advanced machine learning and artificial intelligence to identify and mitigate threats based on their behavior.
Key Features of the Sentinel One Agent
The Sentinel One Agent comes packed with a variety of features that make it a standout in the cybersecurity landscape. Some of the key features include:
- Real-Time Threat Detection: The agent continuously monitors endpoints for suspicious activities and potential threats, providing immediate alerts and responses.
- Automated Response: Once a threat is detected, the Sentinel One Agent can automatically take actions to neutralize it, such as isolating the affected endpoint or terminating malicious processes.
- Behavioral Analysis: By analyzing the behavior of files and processes, the agent can identify and block threats that traditional antivirus software might miss.
- Machine Learning: The agent leverages machine learning algorithms to continuously improve its threat detection capabilities, adapting to new and emerging threats.
- Endpoint Visibility: Provides comprehensive visibility into all endpoints, allowing administrators to monitor and manage security across the entire network.
- Compliance and Reporting: Offers detailed reporting and compliance features, helping organizations meet regulatory requirements and internal security policies.
Deployment and Configuration
Deploying the Sentinel One Agent is a straightforward process that can be completed in a few simple steps. Here’s a guide to help you get started:
Step 1: Create an Account
Before you can deploy the Sentinel One Agent, you need to create an account on the Sentinel One platform. This will give you access to the management console where you can configure and monitor your endpoints.
Step 2: Download the Agent
Once your account is set up, you can download the Sentinel One Agent from the management console. The agent is available for various operating systems, including Windows, macOS, Linux, and mobile platforms.
Step 3: Install the Agent
After downloading the agent, you can install it on your endpoints. The installation process is simple and can be done manually or through automated deployment tools. For large-scale deployments, you can use scripts or group policies to install the agent on multiple endpoints simultaneously.
Step 4: Configure Policies
Once the agent is installed, you can configure policies to define how it should behave on your endpoints. This includes setting detection and response rules, defining exclusion lists, and configuring reporting settings. The management console provides a user-friendly interface for creating and managing these policies.
Step 5: Monitor and Manage
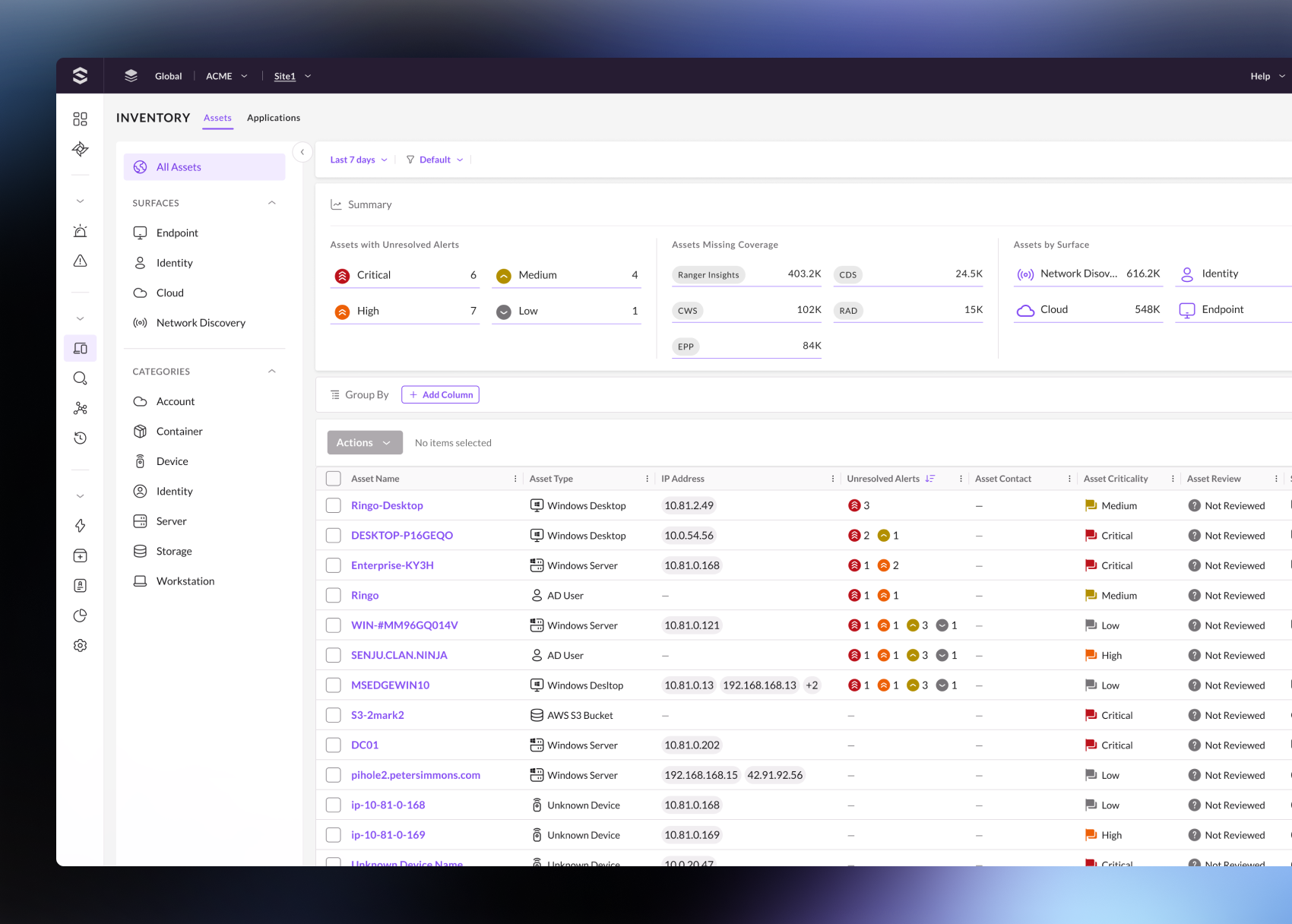
With the Sentinel One Agent deployed and configured, you can monitor your endpoints in real-time through the management console. The console provides detailed insights into threat activity, endpoint status, and overall security posture. You can also generate reports and alerts to stay informed about potential threats and security incidents.
🔒 Note: Ensure that you regularly update the Sentinel One Agent to benefit from the latest threat intelligence and security features.
Benefits of Using the Sentinel One Agent
The Sentinel One Agent offers numerous benefits that make it a valuable addition to any organization’s cybersecurity strategy. Some of the key benefits include:
Enhanced Threat Detection
The agent’s advanced machine learning and behavioral analysis capabilities enable it to detect and respond to threats that traditional antivirus software might miss. This includes zero-day threats, fileless malware, and other sophisticated attacks.
Automated Response
With automated response capabilities, the Sentinel One Agent can quickly neutralize threats before they cause significant damage. This reduces the need for manual intervention and ensures that threats are addressed promptly.
Comprehensive Visibility
The agent provides comprehensive visibility into all endpoints, allowing administrators to monitor and manage security across the entire network. This includes detailed insights into threat activity, endpoint status, and overall security posture.
Scalability
The Sentinel One Agent is designed to scale with your organization, making it suitable for both small businesses and large enterprises. Whether you have a few endpoints or thousands, the agent can be deployed and managed efficiently.
Compliance and Reporting
The agent offers detailed reporting and compliance features, helping organizations meet regulatory requirements and internal security policies. This includes generating reports on threat activity, endpoint status, and overall security posture.
Use Cases for the Sentinel One Agent
The Sentinel One Agent can be used in a variety of scenarios to enhance cybersecurity. Some common use cases include:
Endpoint Protection
Protecting endpoints from malware, ransomware, and other cyber threats is a primary use case for the Sentinel One Agent. By continuously monitoring endpoints for suspicious activities, the agent can detect and respond to threats in real-time.
Incident Response
In the event of a security incident, the Sentinel One Agent can provide valuable insights and automated responses to help mitigate the impact. This includes isolating affected endpoints, terminating malicious processes, and generating detailed reports on the incident.
Compliance Management
Organizations often need to comply with various regulatory requirements and internal security policies. The Sentinel One Agent offers detailed reporting and compliance features, helping organizations meet these requirements and demonstrate their security posture.
Remote Workforce Security
With the rise of remote work, securing endpoints outside the traditional network perimeter has become increasingly important. The Sentinel One Agent can be deployed on remote endpoints to provide comprehensive security and visibility, ensuring that remote workers are protected from cyber threats.
Best Practices for Using the Sentinel One Agent
To maximize the effectiveness of the Sentinel One Agent, it’s important to follow best practices for deployment and management. Here are some key best practices to consider:
Regular Updates
Ensure that the Sentinel One Agent is regularly updated to benefit from the latest threat intelligence and security features. This includes updating the agent software and configuring policies to reflect the latest threat landscape.
Policy Configuration
Configure policies to define how the agent should behave on your endpoints. This includes setting detection and response rules, defining exclusion lists, and configuring reporting settings. Regularly review and update these policies to ensure they remain effective.
Monitoring and Alerts
Monitor your endpoints in real-time through the management console and configure alerts to stay informed about potential threats and security incidents. This includes setting up notifications for critical events and generating detailed reports on threat activity.
Incident Response Planning
Develop an incident response plan that outlines the steps to take in the event of a security incident. This includes defining roles and responsibilities, establishing communication protocols, and configuring automated responses through the Sentinel One Agent.
Training and Awareness
Provide training and awareness programs for your employees to educate them about cybersecurity best practices and the importance of the Sentinel One Agent. This includes teaching them how to recognize and report potential threats and how to use the agent effectively.
Comparing the Sentinel One Agent with Traditional Antivirus Software
While traditional antivirus software has been a staple in cybersecurity for many years, it often falls short in detecting and responding to modern threats. Here’s a comparison of the Sentinel One Agent with traditional antivirus software:
| Feature | Sentinel One Agent | Traditional Antivirus Software |
|---|---|---|
| Threat Detection | Behavioral analysis and machine learning | Signature-based detection |
| Response Time | Real-time threat detection and automated response | Delayed response, often requiring manual intervention |
| Zero-Day Threats | Effective detection and response | Limited or no detection |
| Endpoint Visibility | Comprehensive visibility and monitoring | Limited visibility and monitoring |
| Compliance and Reporting | Detailed reporting and compliance features | Basic reporting and limited compliance features |
As shown in the table, the Sentinel One Agent offers significant advantages over traditional antivirus software, making it a more effective solution for modern cybersecurity challenges.
🔒 Note: While traditional antivirus software can still be useful as a supplementary layer of security, it should not be relied upon as the primary defense against cyber threats.
Future Trends in Endpoint Security
The landscape of endpoint security is continually evolving, driven by advancements in technology and the increasing sophistication of cyber threats. Some future trends to watch out for include:
Advanced Machine Learning
Machine learning algorithms will continue to improve, enabling more accurate and efficient threat detection. This will allow the Sentinel One Agent to stay ahead of emerging threats and adapt to new attack vectors.
Behavioral Analysis
Behavioral analysis will become even more sophisticated, allowing the agent to identify and respond to threats based on their behavior rather than relying on signatures. This will enhance the agent’s ability to detect and mitigate zero-day threats and other advanced attacks.
Integration with Other Security Tools
The Sentinel One Agent will likely integrate more seamlessly with other security tools and platforms, providing a comprehensive security ecosystem. This will enable organizations to leverage multiple layers of security and enhance their overall defense posture.
Cloud-Based Security
As more organizations move to the cloud, cloud-based security solutions will become increasingly important. The Sentinel One Agent will continue to evolve to provide robust security for cloud-based endpoints, ensuring that organizations can protect their data and applications in the cloud.
Automated Incident Response
Automated incident response capabilities will become more advanced, allowing the agent to take immediate and effective actions to neutralize threats. This will reduce the need for manual intervention and ensure that threats are addressed promptly.
In conclusion, the Sentinel One Agent represents a significant advancement in endpoint security, offering comprehensive protection against a wide range of cyber threats. By leveraging advanced machine learning, behavioral analysis, and automated response capabilities, the agent provides real-time threat detection and response, ensuring that your organization’s endpoints are safeguarded. With its scalability, compliance features, and detailed reporting, the Sentinel One Agent is a valuable addition to any organization’s cybersecurity strategy. As the threat landscape continues to evolve, the Sentinel One Agent will remain at the forefront of endpoint security, providing the protection and visibility needed to stay ahead of emerging threats.
Related Terms:
- sentinel one agent update
- sentinel one agent version
- sentinel one agent linux
- download sentinel one agent
- sentinel one agent icon
- sentinel one agent uninstall